Georgia Tech-Savannah
Bringing Professional Education to Coastal Georgia
Providing professional education to adult learners for over a century in Georgia and a decade in Savannah, Georgia Tech-Savannah continues to serve as the Institute's lifelong learning arm. From education for veterans to K12 STEM enrichment and outreach, leadership training, OSHA training, and applied research, Georgia Tech-Savannah offers professional education courses and community outreach for individuals and businesses in the Coastal Empire and surrounding region.
Conveniently located off of I-95 on the Jimmy DeLoach Parkway, the Georgia Tech-Savannah campus is also home to the region's Enterprise Innovation Institute's office for the Advanced Technology Development Center (atdc), Georgia Tech Manufacturing Extension Partnership (GaMEP), and the Georgia Tech Procurement Assistance Center (gtpac). In addition, the Savannah campus serves as location for the Center of Innovation for Logistics.
Georgia Tech-Savannah is bringing the world to Savannah
Explore Our Professional Offerings
We offer a variety of professional development courses to build your skills, deepen your knowledge, and set yourself up for success in your career.
Read MoreWe ensure students in the Savannah area receive the best preparation in science, technology, engineering, and mathematics through our K12 programs.
Read MoreOur leadership training provides Savannah-area professionals the knowledge to meet current and future business needs of the coastal region.
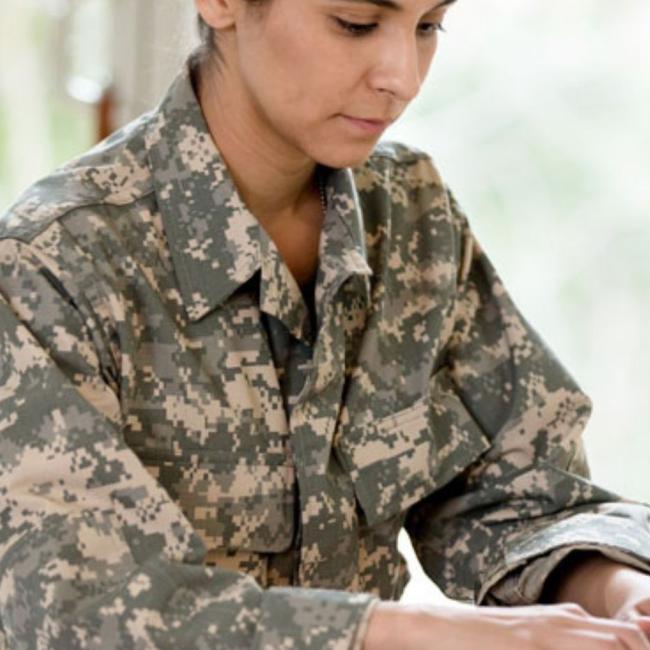
Read MoreOur fully-funded military transition program prepares veterans, active-duty service members, and military spouses for jobs in the civilian world.
Read MoreCommunity Impact
Helping the coastal region evolve and excel through our unique programs, community partnerships, and industry expertise.
of professionals benefit from our professional development programs.
K-12 students served in Savannah and surrounding region by CEISMC.
of VET2 graduates receive full-time job offers from partner businesses.